Learn what managed IT support is and how HenkTek helps Fort Myers small businesses stay protected, productive, and running smoothly....
If you run a small business, your computers and servers hold everything that matters — client records, invoices, project files, photos, emails, and the data that keeps your operation running day to day. Now imagine losing it all in a single afternoon. A hard drive fails. Ransomware encrypts your f...
October is Cybersecurity Awareness Month, and it’s a great reminder for local businesses to tighten things up before something slips through the cracks. You don’t need to be a tech expert to keep your data safe — just a few smart habits go a long way. Here are five simple “wins” that make ...
Why having great tech support should be important to small businesses. As a small business owner, you know that every penny counts. You also know that your time is valuable, and you can’t afford to waste it on IT problems. That’s why having great tech support is so important. Here are...
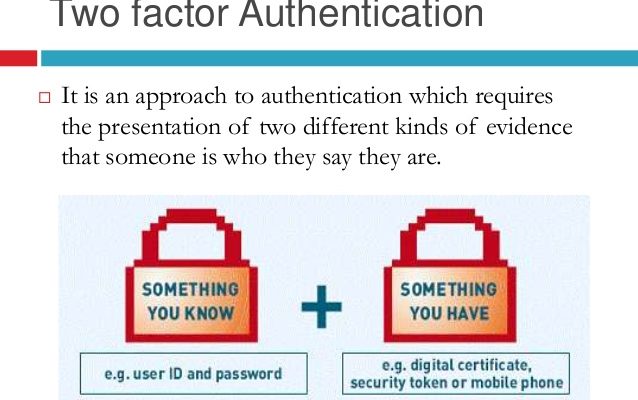
Here are some IT security recommendations for employees in a small business: Use strong passwords, and change them regularly. A strong password is at least 12 characters long and includes a mix of upper and lowercase letters, numbers, and symbols. Enable multi-factor authentication (MFA) whenever po...
Here are some tips to Protect Your Devices from viruses, malware, and ransomware: Be careful about what links you click on in emails and on websites. Vigilance is crucial when interacting with links in emails and on websites. If uncertainty lingers regarding a link’s safety, it’...
In today’s digital age, cyber threats loom large. From viruses to ransomware, we face unseen adversaries online. This article explores the “Cyber Security Threats of Today” and offers protection insights. Viruses: Viruses are a type of malware that can replicate themselves and spr...
As our reliance on digital platforms and online activities continues to expand, so does the need for enhanced security measures. The ever-evolving methods of cyberattacks and the potential risks associated with unauthorized access demand robust safeguards for protecting our sensitive information and...