A Fort Myers accounting firm found out the hard way last spring. An employee reused the same password for their work email and a shopping site that got breached in 2024. Attackers grabbed those credentials off a dark web marketplace for about $12, logged into the company email, and redirected two client wire transfers before anyone noticed. Total damage: north of $87,000.
This isnt some rare edge case. Credential theft is now the single most common way attackers break into small businesses, and it’s happening across Southwest Florida more than most owners realize. The 2025 Verizon Data Breach Investigations Report found that 71% of web application breaches involved stolen credentials. Not fancy zero day exploits. Not nation state hackers. Just usernames and passwords that employees used somewhere else and that ended up for sale online.
How Your Passwords End Up on the Dark Web
It starts with a data breach at some company you’ve probably forgotten you even signed up for. Maybe it was a fitness app, a food delivery service, or some random forum from 2019. When that company gets hacked, the attackers dump millions of email and password combinations into databases that get traded and sold on dark web marketplaces.
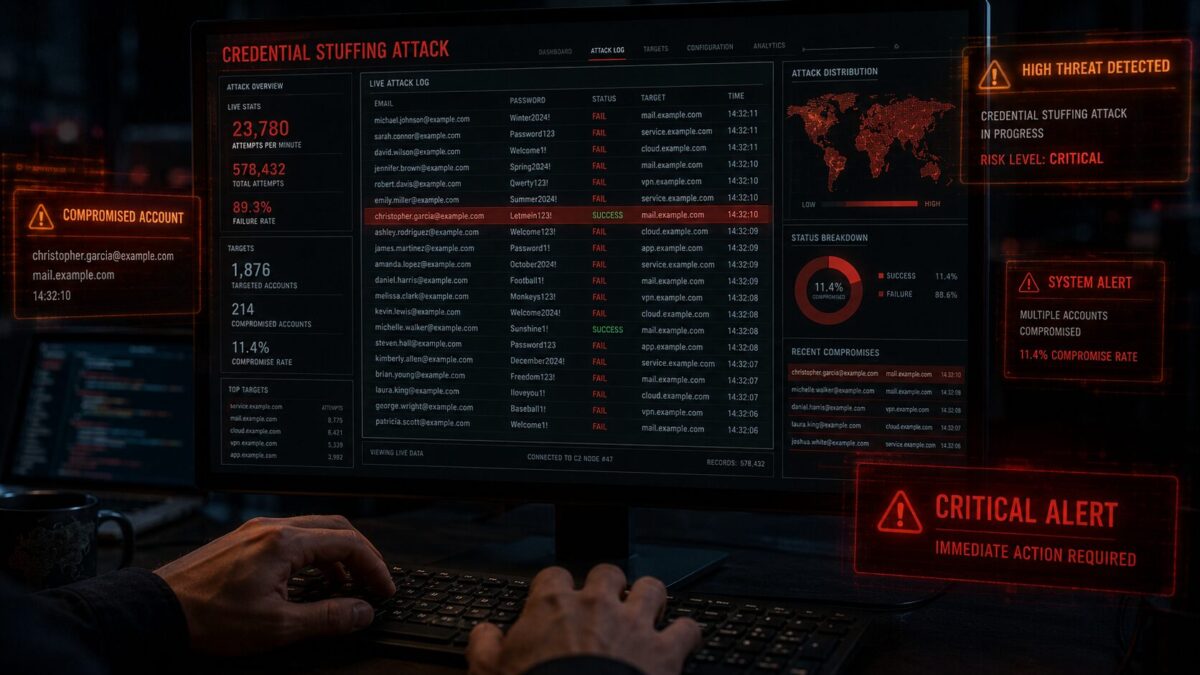
The problem? Most people reuse passwords. A 2024 study by SpyCloud found that 61% of breached users had reused the same password across multiple accounts. So when that fitness app password turns out to be identical to your work email password, attackers dont even have to try hard. They just plug stolen credentials into business email portals, VPNs, and cloud apps using automated tools. This is called credential stuffing, and its shockingly effective.
For businesses in Fort Myers and Cape Coral, this hits especially hard. Smaller companies typically dont have dedicated security teams monitoring for compromised credentials. By the time you find out, the damage is already done.
Credential Stuffing Attacks Are Spiking in 2026
The numbers are ugly. Cybersecurity researchers tracked a 34% increase in credential stuffing attacks targeting small and mid sized businesses in the first quarter of 2026 alone. And these arent sophisticated operations. Attackers buy lists of stolen credentials for pennies per record and run them through automated bots that can test thousands of login combinations per minute.
What makes this worse for Fort Myers businesses: many local companies still rely on basic email and password combos without multi factor authentication. Some are using the same admin passwords theyve had since they set up their systems five years ago. Attackers know this. They specifically target smaller markets where security budgets are tighter and IT oversight is thinner.
The FBI’s Internet Crime Complaint Center reported that business email compromise scams alone transferred more than $6.3 billion from victims recently. A huge chunk of those attacks started with stolen credentials, not clever hacking.
How to Check If Your Business Credentials Are Already Exposed
Heres the thing that surprises most business owners: you can actually check. Services like Have I Been Pwned let you search email addresses against known breach databases for free. If your work email shows up (and honestly, it probably will), that doesnt necessarily mean you’ve been hacked. But it means your credentials are floating around out there, and if you haven’t changed that password since the breach, you’re a sitting target.
For a more thorough check, dark web monitoring services continuously scan underground marketplaces and forums for your company’s email addresses, domain names, and credentials. This is something we set up for our managed IT clients here in Fort Myers, and the results are usually eye opening. Most businesses have at least a handful of exposed credentials they didn’t know about.
5 Things Fort Myers Businesses Should Do This Week
You dont need a massive IT budget to close this gap. Here are the moves that actually matter:
1. Turn on multi factor authentication everywhere. MFA is the single best defense against stolen credentials. Even if an attacker has your password, they cant get in without that second factor. Start with email, then expand to VPNs, cloud storage, and any business apps. Microsoft 365 and Google Workspace both include MFA for free. Theres no excuse not to use it.
2. Run a dark web scan on your company domain. Find out whats already out there. If employee credentials show up in breach databases, force password resets for those accounts immediately. Dont wait.
3. Kill password reuse with a business password manager. Tools like Bitwarden or 1Password for Business generate unique passwords for every account and store them securely. Your employees wont need to remember anything, and they wont be tempted to reuse passwords across sites. Setup takes about an hour for a small office.
4. Set up login monitoring and alerts. Most cloud platforms can flag unusual login activity, like someone accessing your email from a new country at 3am. These alerts are usually free to enable but almost nobody turns them on. Takes about 15 minutes to configure in Microsoft 365 or Google Workspace.
5. Train your team on password hygiene. Not a boring annual PowerPoint. Just a quick 20 minute conversation about why reusing passwords is dangerous, how to spot phishing attempts that steal credentials, and what to do if they think their account is compromised. Real talk, not corporate compliance theater.
What Happens If You Ignore This
The math is pretty straightforward. The average cost of a data breach for a small business in 2025 was around $164,000 according to IBM. For a 20 person company in Bonita Springs or Naples, that could be enough to shut the doors. And most of these breaches started with something as simple as a reused password.
Insurance isnt a safety net either. Cyber insurance providers in 2026 are requiring MFA, password policies, and regular security assessments as conditions of coverage. If you cant prove you had basic protections in place, your claim might get denied. We’ve seen this happen to businesses right here in Southwest Florida.
Need Help Locking This Down in Fort Myers?
At HenkTek, we help small businesses across Fort Myers, Cape Coral, Bonita Springs, and Naples get their credential security sorted out. That includes dark web monitoring, MFA setup, password manager deployment, and ongoing security monitoring so you’re not flying blind.
If you’re not sure where your business stands, we offer a free security assessment. Give us a call at (239) 234-2334 or reach out through our contact page and we’ll take a look at whats going on.
Stolen credentials arent going away. But you can make sure yours arent the easy target.